General Information
Over 15% of new users switched from Websense. Over 20% used to run Surf Control. Ask about our competitive pricing program and find out why it literally pays to switch your Web filter to Pearl Software.
QUICK TOUR
View short videos about Pearl Echo's cybersecurity features and ease of installation.REQUEST A QUOTE
Contact the Pearl Software sales team to learn about Pearl Echo.Suite pricing options.COMPARE PRODUCTS
See how Pearl product specifications meet your requirements.
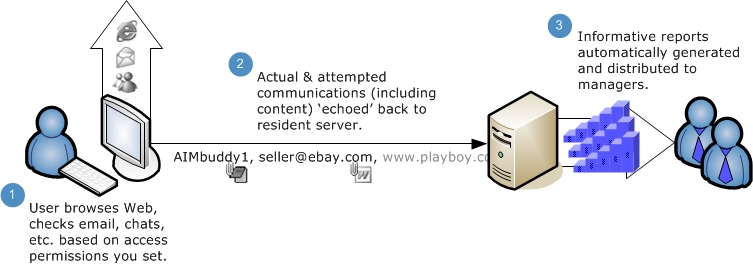
For peer-to-peer, server-centric and client-server computing environments, you'll be able to set user-level policies for monitoring usage and controlling Internet access across your network. By using Pearl Echo.Suite web monitoring software, administrators can filter and monitor a variety of activities including e-mail, IM, chat, news, the transferring of files and browsing the Internet. If you change Internet applications, Pearl Echo.Suite will not be affected since cybersecurity rules are applied at the protocol level.
This comprehensive application gives you even more control by allowing you to track keyword usage and text patterns. This enables you to prevent confidential information from leaking out in blog and web postings, e-mail, instant messenger communications and also in e-mail attachments that are encoded.
If you want to know the amount of time users are engaged in online, a mouse click in Pearl Echo.Suite will tell you. Go deeper in your analytics with a best-in-class report manager that lets you link to content that users have accessed or automatically restore the content from e-mails, news group postings and instant messenger activities - both inbound and outbound. You'll have more than 75 standard, customizable reports that you can set up to run interactively or be generated and distributed automatically.
The software's mobile technology is ideal for organizations that want their policies for Internet use to cover not only their internal network but also to extend beyond it. If you have thick client workstations or thin client workstations using Terminal Services or Citrix, Pearl Echo.Suite is the perfect application. While this powerful cybersecurity product is surprisingly easy to deploy, it provides exactly what's needed for today's network infrastructures that are both complex and ever-evolving.
Pearl Echo.Suite is an incredibly feature-rich package. Some of the latest features include:
- Echo Crypto.View™ - Monitor encrypted communications. Secure sites act just like regular web sites. They can still be filtered the same way and by the same rules. The same is true for secure email. Safely view and control encrypted data (https, ssl, etc.) without the use of complicated proxy servers or Internet traffic redirection.
- Echo Smart.Capture™ - Focus on user trends while reducing monitoring and storage of non-pertinent user web activity by as much as 96%.
- HTTPSafety.Check™ - Ensure the strength of encrypted communications.
- Safe Search - Enforce Google, Bing and Yahoo Safe Search settings.
- Workstation Installation Automation - Remotely deploy Pearl Echo agents from your Pearl Echo Administration Console.
- DLP for Skype - Identify, monitor, and automatically protect sensitive information in Skype for Business.
- Web Crawler - Easily create Allow Lists with a built in search tool to identify hidden resources needed to load pages.
- Profile Investigator - Quickly report on users' profiles and active cybersecurity rules.
- Web Page Redirect - Customize what a browser displays when a user is blocked due to a security restriction.
- Advanced Report Filters - Create unlimited filters for additional report customization and more granular analytics.
- Report Classification Headings - Add customized DoD-compliant document markings with appropriate security descriptors.
- Zero 3rd-party conflicts - Run with confidence. Pearl Echo's patented cybersecurity technology integrates with Microsoft's new firewall security model.
For an exhaustive list of features, select "Show More Details" at the bottom of the Product Comparison Page.
Pearl Echo.Suite Web Filtering Software Requirements
Workstations
- Agent Workstation Hardware Requirements
- Processor and Memory as specified by minimum Operating System requirements.
- At least 100 MB of available disk space.
- Agent Workstation Operating System Compatibility (32 or 64 bit, Host or Virtualized)
- Windows 10, Windows 8, Windows 7
- Windows Server 2019
- Windows Server 2016
- Windows Server 2012, 2012 R2
- Windows Server 2008 R2
- Citrix Server, Microsoft Terminal Server (RDS)
Server Hardware Recommendations (Administration Machine)
- A Windows server or workstation with a fixed IP address or Fully Qualified Domain Name (FQDN).
- Example hardware specifications for a mid-size implementation (250 users) include:
- Processor and Memory as specified by minimum Operating System requirements.
- 1 GB RAM
- At least 10 GB of free disk space
- Operating Systems Compatibility (32 or 64 bit, Host or Virtualized)
- Windows Server 2019
- Windows Server 2016
- Windows Server 2012, 2012 R2
- Windows Server 2008, 2008 R2
- Windows 10
- Windows 8
- Windows 7
Pearl Echo.Suite Web Filtering Software Benefits
Forrester Research finds that one in every 10 Websites is infected with malware.
Dow Chemical fires 24 employees and disciplines hundreds of others for storing and sending sexual or violent images on the company's computers.
Chevron Corporation monitors its employees' visits to cyber space; 46% were irrelevant to their jobs.
While businesses weigh the pros and cons of hooking up their employees to the Internet, executives are taking notice of Internet abuse. Employee Internet misuse and abuse is on the rise leading to computer-related firings and a growing climate of corporate misunderstanding and mistrust. Accessing pornography, chatting, gambling, investing and online shopping are the leading causes for disciplinary action or termination. Major concerns for managers are legal liability, security and reduced worker productivity. The latest business trends show a rise in the number of wrongful termination suits based upon an employer's inability to support accusations of Internet abuse or not having a clear Internet Acceptable Use Policy in place.
Pearl Echo.Suite Benefits
Increases productivity by reducing nonproductive Internet usage
Ensures a positive environment by eliminating inappropriate Internet use
Reduces the risk of unauthorized transactions and communication of sensitive data
Increases management's awareness by providing informative reports that are automatically generated and distributed
Preserves access bandwidth for planned and intended use
Simplifies administration by creating custom Internet access profiles based on existing Directory users, groups and computers
Maintains accountability by sensing access violations and archiving information for future retrieval
Supports your Acceptable Use Policy and allows you to display your standards if a user does not adhere to your policy.
Categorizes surfing habits and provides insight into the amount of time and cost users spend on the web
More Info
Details
Architecture
Configuration
Crypto.View™
Echo.Filters™
Reports
Mobility Monitor™
HTTPSafety.Check™
Citrix & Terminal Server
SQL Server
Product Data Sheet
Product Pricing and Comparison
Support & Updates
Pearl Echo FAQ
Knowledge Base
Product Patches
User's Guide
Sample AUP
Starter Block Lists
