A Targeted Cybersecurity Solution to managing Skype for Business IM and Chat Usage
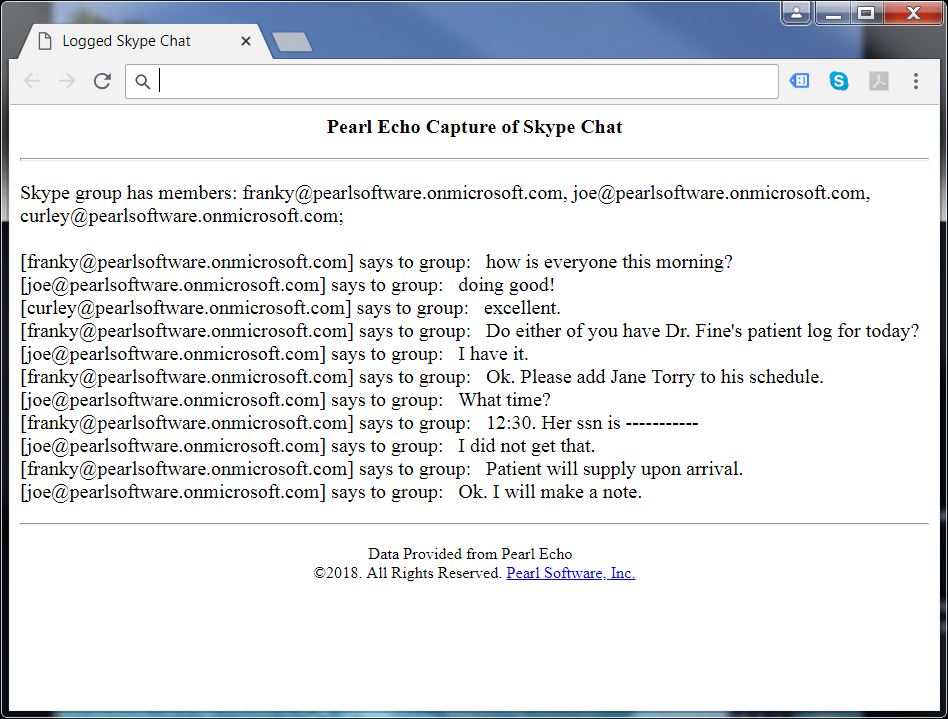
IM.Echo allows you to log and control Skype that is hosted "on-prem" (Lync) or as part of Office 365. IM.Echo's Quick Link™ feature restores the text of incoming and outgoing Chat and IM items, allowing you to maintain a history of all activity for review.
Enterprise-Ready
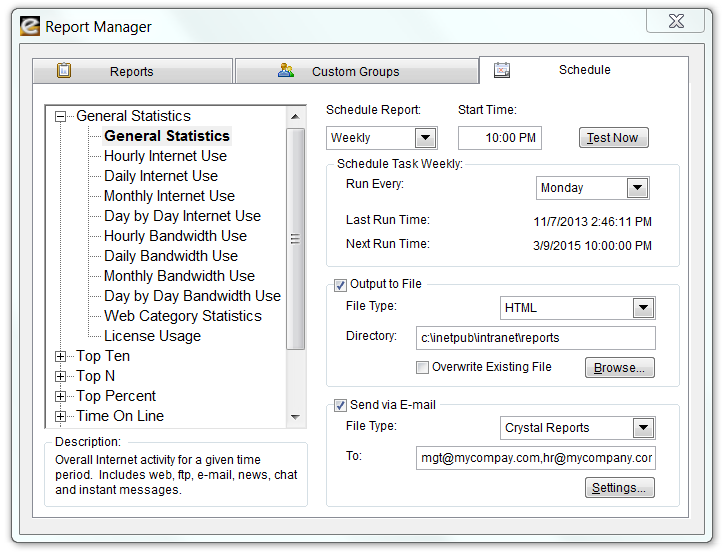
IM.Echo was designed with the enterprise in mind. The IM.Echo Report Manager consists of informative reports that can be customized for your existing Domain users and groups. The Pearl Echo Report Manager allows users to run reports interactively or to schedule reports to be automatically generated and distributed. For larger data handling needs, IM.Echo easily integrates with MS SQL Server. If your organization includes a server-centric computing environment, keep in mind that IM.Echo is the only chat and IM management software that is certified and fully functional in a Citrix & Microsoft Remote Desktop Services environment.
Grows with your Business
IM.Echo is packed with features for the large enterprise but remains based upon the core needs of your growing business. Features like automated deployment, an intuitive standards-based administration console, server-optional setup and self-administering workstation agents allow IM.Echo to meet the needs of any size organization.Protects
Organizations need to protect sensitive information and prevent its inadvertent disclosure. Examples include financial data or personally identifiable information (PII) such as credit card numbers, social security numbers or health records. With IM.Echo’s data loss prevention (DLP) for Skype, you can identify, monitor, and automatically protect sensitive information.
Pearl Echo acts as the enforcement behind your organization's Acceptable Use Policy. Unlike shims that require an .msg dump, all communications can be archived for rapid and organized retrieval, protecting organizations from laws suits related to false termination, discrimination-based claims and regulation compliance.
Secures
IM.Echo provides a secure installation option to protect against unauthorized circumvention. IM.Echo is so efficient that users notice no degradation of access speeds and detect no obvious process or files on their workstations.
Controls
IM.Echo provides administrator-defined Allow and Block lists for instances where Skype IM access needs to be limited. IM.Echo also allows you to set various IM access profiles based on time of day - perfect when you need to provide some flexibility for your day-extenders.Provides Complete Flexibility
Managed users can be connected to your local area network, wide area network, or be completely detached from your private network. IM.Echo runs as an independent service eliminating reliance on legacy proxy servers or integration issues with firewalls or multiple subnets. IM.Echo's architecture scales well and allows you to monitor any form of Internet connection - anywhere. IM.Echo manages Internet access by Windows user, group and computer names. Administration is streamlined by optionally integrating into your Windows Domain or Stand-alone server structure. Unlimited access Profiles can be created to provide varying levels of management for your existing Directory users, groups and computers.
Download a Free Trial ...to get a hands-on look at Pearl Echo's features and functions
Start the Pearl Echo.Suite Product Video Tour ...to get a quick look at Pearl Echo's capabilities without installing.
View Pearl Software vs. Competition ...to see how Pearl Software stacks up to the competition.
Request a Quote ...to receive personalized pricing that matches your requirements.