Local Area Network or VPN Configuration
The computer on which you install IM.Echo Server Software must have an IP address that is visible to managed workstations. When you run IM.Echo for the first time, the Setup Wizard will ask you the IP address of your server and a service port number.
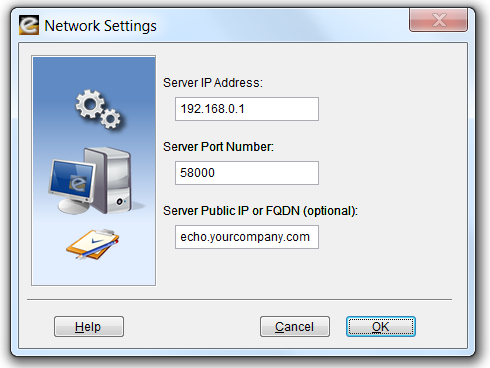
This IP address and port number will also be used during your automated workstation installations. If you would like to monitor users that roam beyond the perimeter of your private network, enter the Public IP or Fully Qualified Domain Name of your IM.Echo Server.
Wide Area Network Configuration
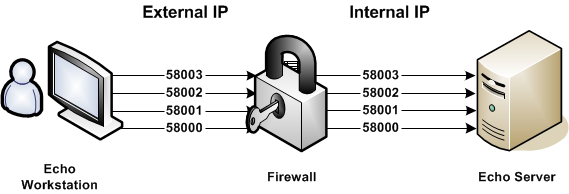
Pearl Software’s Mobility Monitor™ works with a Firewall or NAT device through a specified group of ports. IM.Echo workstations establish an initial connection with the IM.Echo Server on a Control Port (Server Port Number). Additional command and control communications occur on three supplemental IP ports. The Server Port Number (e.g. 58000) and three additional IP ports (e.g. 58001, 58002 and 58003) will need to be opened for direct pass-thru on your Firewall device to manage users while they are off of your private network.
Example
Public IP: Server Port Number + 0 «-» Private IP: Server Port Number + 0
Public IP: Server Port Number + 1 «-» Private IP: Server Port Number + 1
Public IP: Server Port Number + 2 «-» Private IP: Server Port Number + 2
Public IP: Server Port Number + 3 «-» Private IP: Server Port Number + 3
IM.Echo Control Profiles
A control profile is defined by your server's available User, Group and Computer names. When IM.Echo Server Software is installed on a machine that is part of a Domain using the Active Directory Service, IM.Echo will access and display the available User, Group and Computer names from the Active Directory database. If Active Directory Service is not available, IM.Echo will access and display the available User and Group names from the server on which it is installed.
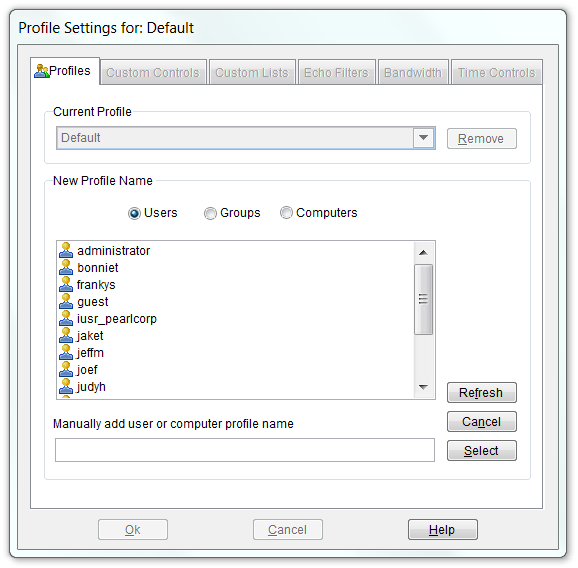
When a managed User attempts to access the Internet, their activity is governed by a Profile’s configuration settings. IM.Echo first looks for a matching User profile. If no matching User profile is found, IM.Echo looks for a Group profile to which the User belongs. If no matching Group profiles are found, IM.Echo looks for a Computer profile based on the computer name being used. If no matching Computer profiles are found, IM.Echo uses the settings defined by your Default profile. If a User belongs to multiple Groups, IM.Echo selects the first matching Group (alphabetically) to govern IM access.
IM.Echo Control Settings
Security levels are established by selecting the appropriate button under the Chat/IM category in conjunction with entries in the Profile's Chat Allow and Block Control Lists. Additional security configurations are available in Pearl Echo.Suite.
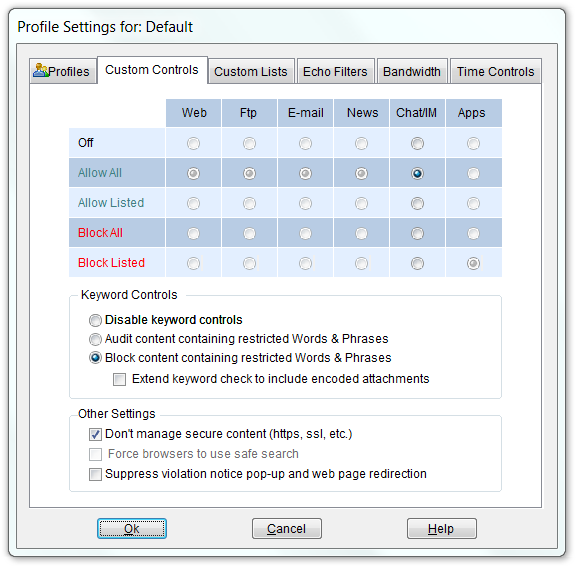
You can have IM.Echo block or audit objectionable words, phrases and text patterns by selecting "Block/Audit content containing restricted Words & Phrases." With the Block option set, IM.Echo will allow all IM activity except for content containing words or phrases defined in the Profile's Words & Phrases Control list.
Download a Free Trial ...to get a hands-on look at Pearl Echo's features and functions
Start the Pearl Echo.Suite Product Video Tour ...to get a quick look at Pearl Echo's capabilities without installing.
View Pearl Software vs. Competition ...to see how Pearl Software stacks up to the competition.
Request a Quote ...to receive personalized pricing that matches your requirements.
